Risks of Not Using A DNS Filter
A DNS filter is an important component of your IT security posture. DNS filters ensure your users are accessing safe domains to reduce the risk of an attack. Learn more about the risks you face without using this security solution.
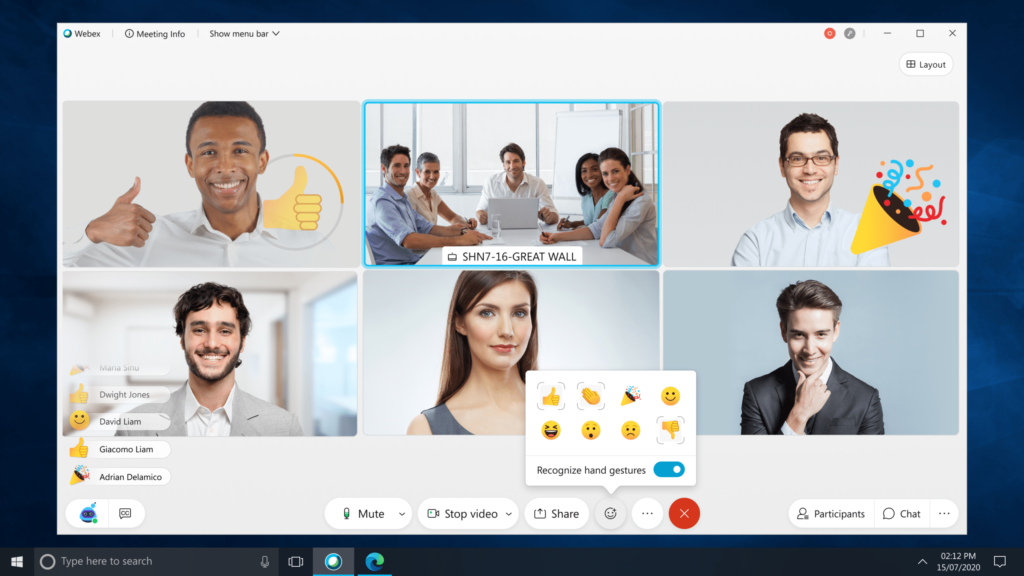
What Webex Looks Like Now
A lot has changed since the beginning of the coronavirus pandemic, including Webex. We review the most significant updates to Webex since video conferencing became more mainstream.
Best Practices for IT Managers Deploying Softphones
Are you an IT manager or CIO considering softphones for your company? There are several steps you can take to make the process go smoothly for your business. Take a look at our best practices to guide your softphone deployment.
IT for Education: Internal vs. Managed vs. Co-Managed IT Services
Finding the right type of IT support is essential for your school’s students and staff. The options of internal IT department, managed services, and co-managed services all have different pros can cons. We’ve put them all here for you to read and decide what’s best for you.
Best Candidates for Softphones
Are you wondering if softphones are right for your business? We’ll walk you through five of the most impactful use cases we’ve seen for softphones and explain how they could apply to your business.
How Softphones Can Improve Your Workday
It’s no secret your users’ IT needs have changed since the beginning of 2020. Softphones provide a simple, cost-effective option for your users to continue making and receiving business phone calls while working remotely.
3 Reasons Why Your School Should Consider Managed IT Services
Are you struggling to find an IT support solution that works best for your educational institution? Managed IT services are a great way to support your school’s IT environment because they provide experience, redundancy, and knowledge you need to empower your staff and students.
Pros & Cons of a Defensive IT Security Risk Assessment
Are you looking for an external perspective on the strength of your cybersecurity defenses? A defensive IT security risk assessment looks at the defenses of all areas of your IT environment. This assessment has many pros, but there are also a few cons to consider.
Engaging Cisco Partner Support vs. Cisco TAC Support
When you need support for your Cisco solution, you have the option to engage Cisco’s Technical Assistance Center (TAC) or your Cisco partner. Each option is useful in certain scenarios, and we’ll explain the benefits of engaging Cisco TAC vs. Cisco partner for IT support.
4 Steps to Responding to an IT Security Threat
Do you know how to respond to an IT security threat? Even with security solutions in place, it’s possible to become a victim of an IT security threat. Check out our four steps to help you respond to a cyberattack.
WebexOne Recap: All new Webex, Cisco Calling Plan, & More
An all new Webex and Cisco Calling Plan were two of the collaboration announcements during Cisco’s December WebexOne virtual event. We review the Cisco collaboration solutions you should keep on your radar this year.
How to Plan for Interruption with Collaboration Upgrades & Implementations
No IT director gets excited about downtime, but it’s an inevitable part of regular hardware replacements and software upgrades. Our article goes over ways to ease the pain of interruption, specifically in collaboration, but can be applied to other areas of IT as well.
Get in Touch
Have a question or comment? We’d love to talk. Fill out the form below, and we’ll be in touch with you soon.